
Sehtej Khehra
April 24, 2026
6 min read
Cut code review time & bugs by 50%
Most installed AI app on GitHub and GitLab
Free 14-day trial
Just days ago, Vercel, a widely used cloud platform for deploying web applications, disclosed a breach that began months earlier. It started in a roundabout way, when a Context.ai employee unwittingly installed a Lumma Stealer disguised as a Roblox script.
A Vercel employee, using Context.ai, then unwittingly got caught up in this trap. The attackers harvested the Vercel employee’s Google Workspace credentials via stolen OAuth tokens, then moved laterally and breached Vercel's internal systems. This exposed API keys, tokens, database credentials, signing keys, and more. In response, Vercel advised customers to rotate any environment variable not marked "sensitive" and to treat those values as compromised.
The inevitable post-mortems of this hack will focus on OAuth governance and third-party SaaS risk. Those angles are valid, but they miss the point for security leaders responsible for the code itself: This was a developer supply chain attack, and the stolen assets prove it.
Our customers trust us with their most valuable asset, their source code. That trust is why security isn't an afterthought. It's a CodeRabbit design principle.
The right question isn't whether a component in your developer stack gets breached. The better question is, what's the maximum damage an attacker can do from that point?
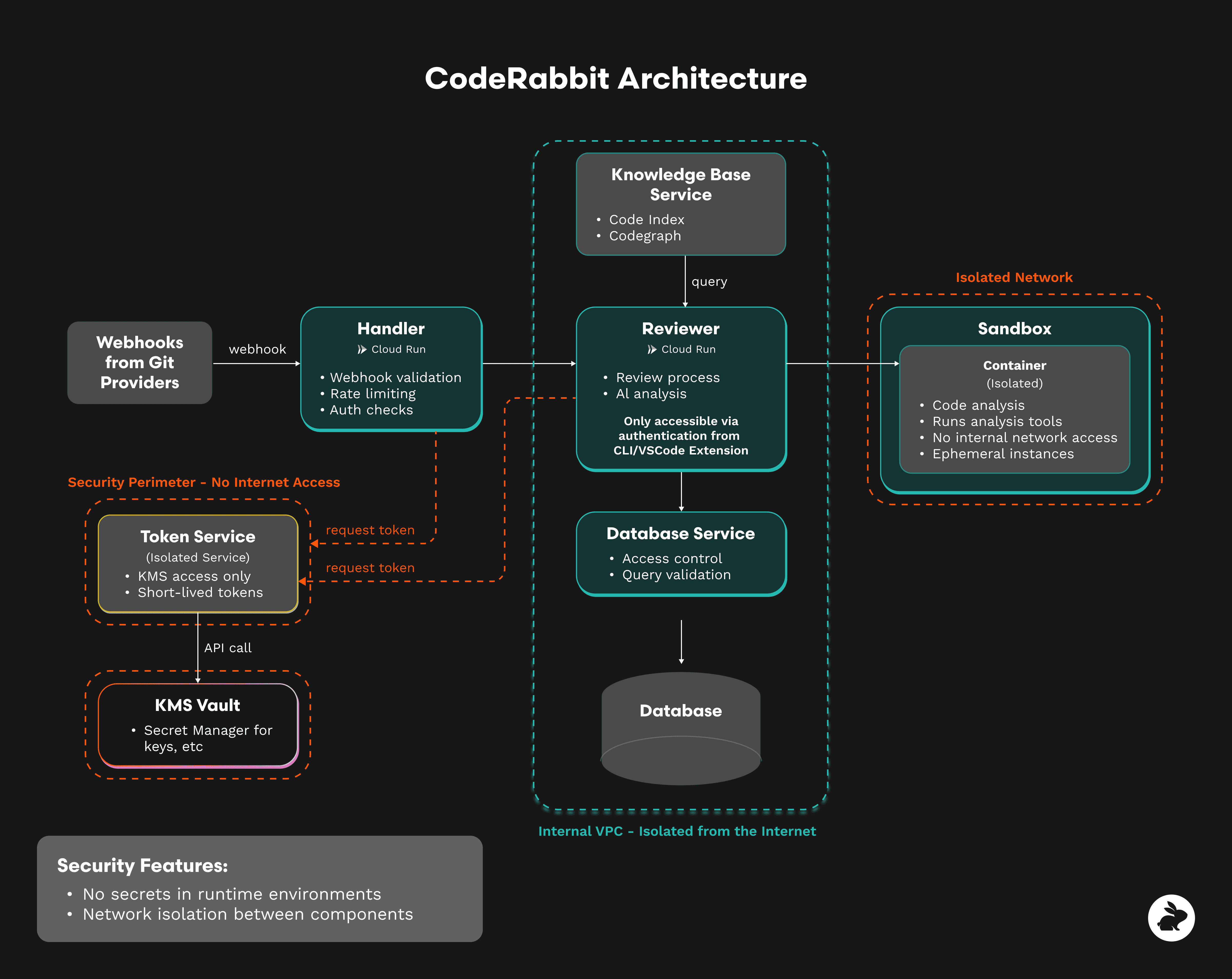
We built the CodeRabbit code-review platform around that question. Every code review runs in an isolated, ephemeral sandbox and is provisioned per event and destroyed after completion. Each sandbox holds a single, short-lived token scoped only to the repository under review. There’s no shared state between customers. There are no long-lived credentials. There’s no access to internal networks.
Sandboxes can reach the public internet when tools require it, but cannot reach CodeRabbit's internal services. Stored code is encrypted with per-customer keys, inaccessible even to CodeRabbit employees.
The result is this: If a sandbox is compromised, there's nothing to pivot to. There’s no persistent tokens, and no lateral movement paths.
If one of your sandboxes or workers is breached tomorrow, what's the worst-case outcome? Every enterprise should ask this of every vendor in their developer stack.
Many Vercel customers had to rotate keys they didn't know were exposed because the most damaging credentials are often the ones teams forget exist, buried in environment variables or hardcoded directly in source files.
Code review is the last practical checkpoint before a secret becomes permanent. Once a credential is committed to a Git repository, it can't be fully scrubbed. Copies persist in forks, caches, CI logs, and developer machines. The only reliable defense is catching it at the pull request.
CodeRabbit flags hardcoded credentials through a combination of pattern matching and AI-powered contextual analysis that understands data flow. Pattern matching catches formats like sk_live_*, AKIA[A-Z0-9]{16}, ghp_[a-zA-Z0-9]{36}, and variables named *_SECRET, *_KEY, or *_PASSWORD.
We also integrate tools like Semgrep, Checkov, Brakeman, and Betterleaks, with one-click fixes surfaced directly in the pull request. Security teams can define custom checks in natural language via .coderabbit.yaml and enforce them as pre-merge gates. Examples include blocking files that hardcode database DSNs or flagging OAuth scopes broader than read:user.
Vercel has since updated its platform so new environment variables default to sensitive. That's a step in the right direction, but it only covers secrets that make it into environment variables. It doesn't catch credentials hardcoded in source files, feature branches, comments, or config files. The more robust approach: treat every credential as sensitive by default, and enforce that at the code review layer before it ever reaches production.
At its core, the Vercel breach was an identity breach. An OAuth token issued to a third-party app became an attacker's access path. Every tool with OAuth access in your workspace, every CI service running on long-lived GitHub tokens, every AI assistant with read access to a monorepo, each of those is a potential entry point.
Your code review platform deserves the same identity rigor you apply to your identity provider.
For CodeRabbit Enterprise, that includes:
The goal is straightforward. Even if something upstream is breached, your code review tool should never be the next entry point in the attack chain.
The Vercel breach is a reminder to reassess every tool that touches your codebase. Ask these questions of any vendor with access to your source code, including us:
CodeRabbit's answers are detailed in our full security architecture, and in our Trust Center. Our team is also happy to answer any questions.
Supply chain attacks don't start at the primary target. They start at the weakest link. Every vendor in your developer workflow, every tool with a token, an OAuth grant, or read access to your code is a potential entry point. The Vercel breach didn't begin at Vercel. It began with a Roblox script.
Demand answers. Every vendor you trust with your source code should be able to tell you exactly what happens if they're the next Vercel.